As additional facets of daily life go digital, it’s more paramount now than ever to be proactive about online security. As 2022 proved, however, staying safe isn’t just a modern concern as vulnerabilities have been around for years – decades, even – and can crop up in the most unexpected places and ways.
Security researchers show off the RTX 4090’s password cracking power
The new GPU significantly reduces the time required to obtain or recover user passwords
Security researcher and password cracker Sam Croley posted benchmarks highlighting the RTX 4090’s password-cracking muscle. Nvidia’s newest flagship GPU shattered the RTX 3090’s previous benchmark records and doubled performance across almost every algorithm tested. The cracked passwords adhered to security best practices and included random letter cases, symbols, and numbers.
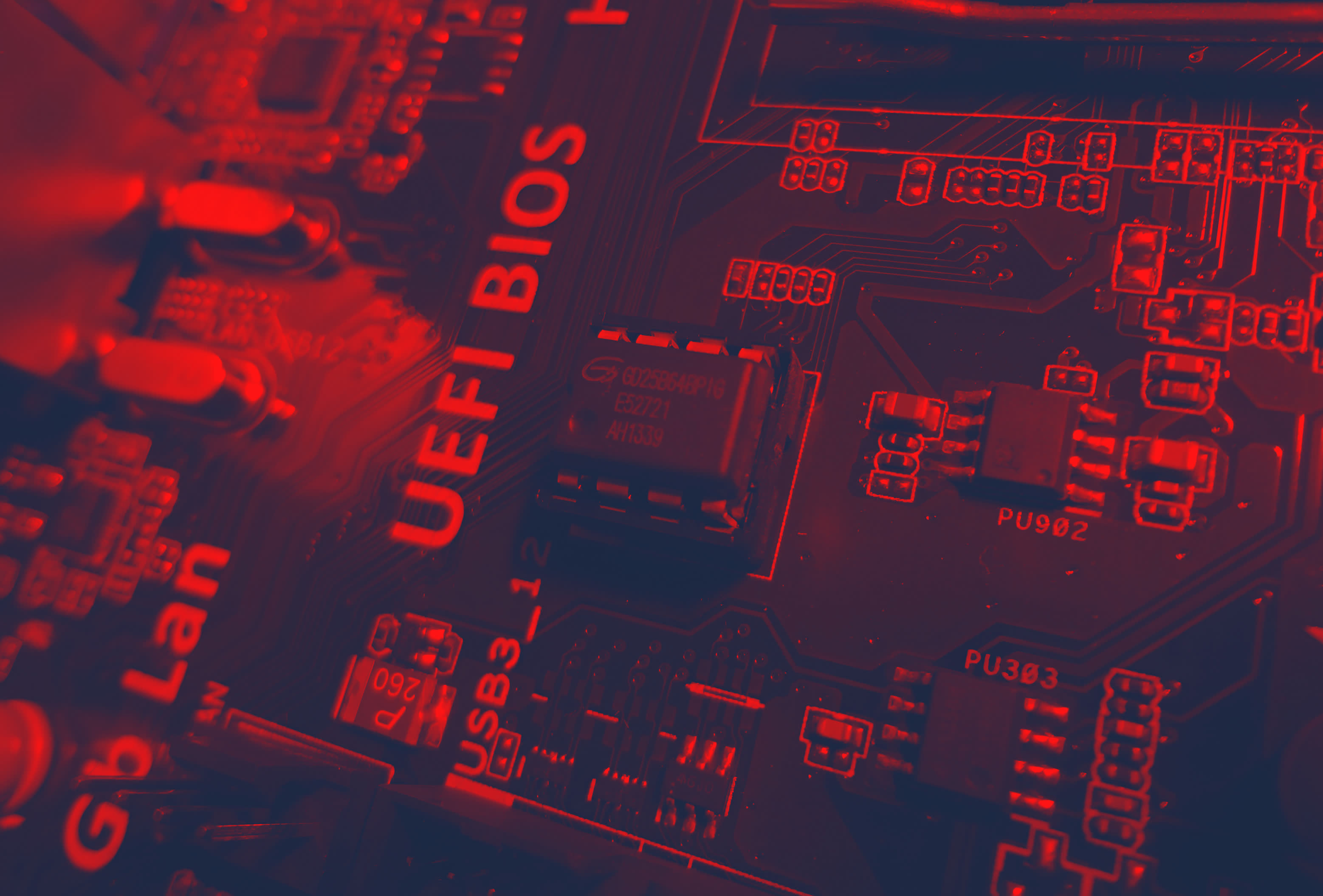
For years, some Gigabyte and Asus motherboards carried UEFI malware
The CosmicStrand rootkit is the latest indication that UEFI malware may be more common than previously thought
Security firm ESET discovered the first UEFI rootkit that had been used in the wild back in 2018. This type of persistent threat used to be the subject of theoretical discussions among security researchers, but over the past years, it’s become clear that it’s a lot more common than previously thought, despite being relatively hard to develop.
Janet Jackson song from 1989 declared a cybersecurity vulnerability for crashing hard drives
Rhythm Nation doesn’t send out good vibrations
People of the world today, are we looking for a better way of life?” sang Janet Jackson on her 1989 hit Rhythm Nation, not knowing that the better way of life she was talking about didn’t include certain hard drives. It’s just been revealed that the song has the power to crash particular models of laptops, and it has now been recognized as a cybersecurity vulnerability.
GameStop “wiretapped” customers without consent, claims lawsuit
It sold secret transcripts to a marketing firm to build profiles using personal information
If it wasn’t stupid enough that GameStop dove headfirst into the NFT and crypto market right before the bubble burst, hang on for a second — the company wants you to hold its beer. It is now being sued for recording customer service chats without consent and selling transcripts to a marketing firm.
QNAP issues ransomware warning to users: secure your devices or disconnect unprotected NAS
Ransomware and brute force attacks from unidentified sources are actively targeting network devices
QNAP issued a security statement urging their NAS users to take immediate action and secure their data against ongoing ransomware and brute force attacks. While the responsible parties have not been identified, the widespread attacks appear to target any vulnerable network devices. The company has provided security setting instructions and mitigation actions that any QNAP NAS users should implement immediately.
Nvidia allegedly hacked its hackers, stole its data back
Hacking group Lapsus$ claims to still have a copy of the data
Several online security groups are reporting that the South American hacker group Lapsus$ is claiming to have been behind the recent cyberattack on Nvidia. It’s also claiming that Nvidia hacked them in return, encrypted the stolen data, and ransomed back their machines. For now, this is just hearsay, but makes for a great turning-the-tables story.
Multiple security flaws emerge in Australian digital driver’s licenses
Possibly less secure than physical ID cards
The government of New South Wales in Australia introduced digital driver’s licenses in late 2019, claiming they were harder to forge than physical identification. A security company recently outlined multiple reasons why this isn’t the case.
Nvidia hackers leak 190GB of sensitive data from Samsung
The leaks includes Samsung’s encryption data and source code
Lapsus$, a hacking group that leaked confidential information from Nvidia just last week, has reportedly moved to a new target: Samsung. The hackers have claimed an attack that leaked 190GB of confidential information from the South Korean technology giant, including encryption data and source code for Samsung’s most recent devices.
Teen hacker gains remote control of over 20 Teslas
Full control over car doors, security system, and more
This week, a teenager reported that he has gained remote access to around two dozen Tesla cars in multiple countries and is trying to contact their owners. The list of things he can do to the affected vehicles is long and dangerous.
Source code for Alder Lake BIOS was posted to GitHub
It could’ve exposed some security vulnerabilities
Apparent source code for Alder Lake BIOS has been shared online. It seems to have been leaked in its entirety at 5.9 GB uncompressed, possibly by someone working at a motherboard vendor, or accidentally by a Lenovo manufacturing partner.